
Right-Size Your Infrastructure with Workload Profiling
IT leaders are tasked with ensuring that IT systems are capable of meeting the needs of users without paying for excess capacity and performance. Considering that systems can reach the end of their lifecycle in as few as five years, right-sizing is far from a one-time challenge.
Undersized systems, by definition, underperform, possibly leading to a compromised perception of the IT function. IT leaders can be left with little choice but to seek additional funds to purchase more compute or storage capacity. Requesting funds for unplanned expenditures can be a bruising proposition in private and public companies, and even more complicated in SLED organizations.
An oversized system sounds harmless enough, on the surface, but that may not be a tenable position for someone being asked to explain why they spent more than needed in the fulfillment of a company’s technology requirements. For SLED organizations, such a misstep risks being labeled as misappropriation of public funds.
Consequences aside, it’s not hard to see how organizations end up with IT solutions that don’t fit. One obvious and all too common scenario occurs when a vendor exploits a perceived lack of expertise on the part of a customer and makes recommendations aimed at increasing the size of the sale. Whether a customer will benefit from additional compute performance or storage capacity is seen as less important in such situations than how much a vendor can profit from a deal.
In situations where customers dictate budget limits—regardless of whether the budget is sufficient for purchasing an appropriately-sized solution—vendors or solution providers may be tempted to deliver an inadequate system just to ensure they get the deal. Truthfully, IT buyers aren’t always open to providers who claim that a more robust—and more expensive—configuration is necessary.
How, then, can organizations avoid acquiring systems that are under- or oversized?
Solving the Right-Sizing Challenge
In our experience, workload profiling is the only effective tactic for right-sizing IT systems. Combining quantitative results compiled by modern workload profiling software with qualitative insights gleaned from a 30-minute Q&A session with a senior IT staffer, Prescriptive has achieved repeatable success in identifying an organization’s practical requirements pertaining to IT. Furthermore, with Prescriptive’s considerable deep and broad experience with products across the IT universe, we’re often able to assemble multiple solution options that both meet organizational requirements and maximize budget effectiveness.
That last sentence is worth revisiting, as it helps explain the value and advantage of working with an experienced solution provider over dealing directly with vendors. Greater knowledge of the IT products universe translates directly into higher likelihood of solution fit.
We generally start our workload profiling efforts with the 30-minute Q&A. We typically ask questions related to growth plans, executive wishlists, user complaints, and anything that we feel may uncover considerations that could impact requirements—current and future—around resource capacity and performance.
With the Q&A complete we’re ready to run profiling tools to determine current workloads. We’re generally assessing the compute stack, storage, backup solutions, or some combination thereof. It’s important to note here that we’re not simply gathering data describing existing resources and their allocation, but rather observing those resources over time in their fulfillment of everyday workloads. Additionally, we want to capture peak loads, and what we learn in the Q&A will help us determine ideal periods in which to conduct effective profiling. Profiling can normally be wrapped up within a week, but in situations where workloads are unpredictable or erratic, we may opt for gathering data for as long as a month.
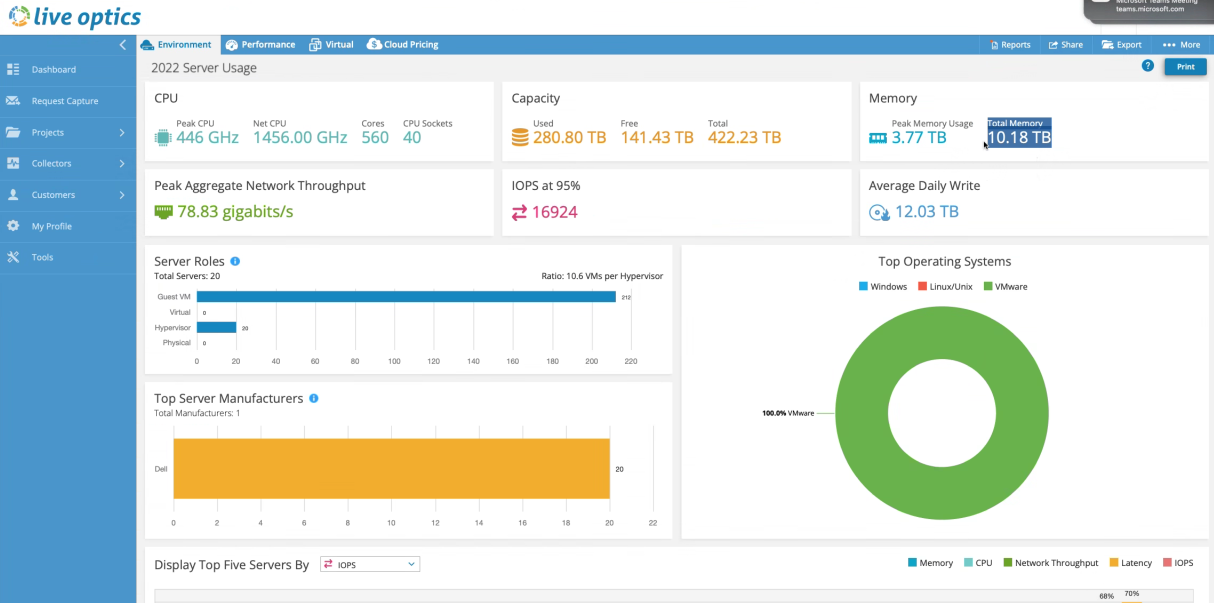
When analyzing workload data, we are, above all, looking for anomalies. If, for example, we notice that an inordinate amount of memory is allocated to a host, we’ll want to dig further to understand why. And with a relatively modest effort, we’ll have the insight needed to size a solution to fit a customer’s workload.
Depending on the situation, our recommendations may involve some level of refactoring to better address workload requirements. “Better”, in this context, generally implies a solution that’s more cost-effective. For backups, in particular, sometimes it’s helpful to redistribute workloads to make more efficient use of existing backup resources. For compute and storage, we’re more likely dealing with right-sizing because we’re at the end of the current technology’s lifecycle. Our client is replacing resources, so squeezing more efficiency from existing resources is not part of the goal. Even so in this case we may want to refactor—not just replace—to deliver a more ideal solution.
In Conclusion
Proper and consistent workload profiling allows us to understand what’s needed, instead of taking for granted what someone might think they need. Rather than enter into an engagement with product recommendations, we prefer to lead with educating our customers on the importance of using data collected through profiling to uncover the best options available and to make decisions that stand the test of time.


.png)
.png)